
Email marketing firm MailChimp disclosed on Sunday that they had been hit by hackers who gained access to internal customer support and account management tools to steal audience data and conduct phishing attacks.
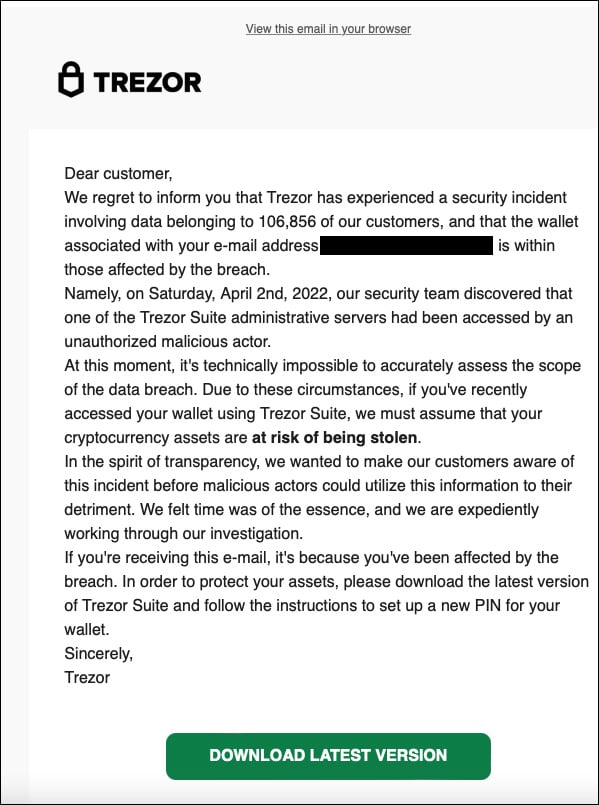
Sunday morning, Twitter was abuzz with reports from owners of Trezor hardware cryptocurrency wallets who received phishing notifications claiming that the company suffered a data breach.
These emails prompted Trezort customers to reset their hardware wallet PINs by downloading malicious software that allowed stealing the stored cryptocurrency.
Source: Twitter
Trezor later shared that MailChimp had been compromised by threat actors targeting the cryptocurrency industry, who conducted the phishing attack.
MailChimp breach targeted crypto, finance
In an email to BleepingComputer, MailChimp has confirmed that the breach was more significant than just Trezor's account being accessed by threat actors.
According to MailChimp, some of their employees fell for a social engineering attack that led to the theft of their credentials.
"On March 26, our Security team became aware of a malicious actor accessing one of our internal tools used by customer-facing teams for customer support and account administration," MailChimp CISO, Siobhan Smyth, told BleepingComputer.
"The incident was propagated by an external actor who conducted a successful social engineering attack on Mailchimp employees, resulting in employee credentials being compromised."
"We acted swiftly to address the situation by terminating access for the compromised employee accounts and took steps to prevent additional employees from being affected."
These credentials were used to access 319 MailChimp accounts and to export "audience data," likely mailing lists, from 102 customer accounts.
In addition to viewing accounts and exporting data, the threat actors gained access to API keys for an undisclosed number of customers, which have now been disabled and can no longer be used.
Application Programming Interface (API) keys are access tokens that allow MailChimp customers to manage their accounts and perform marketing campaigns directly from their own websites or platforms.
Using these compromised API keys, a threat actor can create custom email campaigns, such as phishing campaigns, and send them to mailing lists without accessing MailChimp's customer portal.
Smyth told BleepingComputer that all of the compromised account holders have been notified and that the threat actors accessed customers in the cryptocurrency and finance sectors.
MailChimp says that they received reports of this access being used to conduct phishing campaigns against stolen contacts but have not disclosed information about those attacks..
MailChimp recommends that all customers enable two-factor authentication on their accounts for further protection.
"We sincerely apologize to our users for this incident and realize that it brings inconvenience and raises questions for our users and their customers. We take pride in our security culture, infrastructure, and the trust our customers place in us to safeguard their data. We’re confident in the security measures and robust processes we have in place to protect our users’ data and prevent future incidents."
Siobhan Smyth, Mailchimp’s CISO.
This attack is reminiscent of recent breaches by the Lapsus$ hacking group, who used social engineering, malware, and credential theft to gain access to numerous well-known companies, including Nvidia, Samsung, Microsoft, and Okta.
The Okta breach was accomplished through a similar method as MailChimp, by social-engineering a contractor who had access to internal customer support and account management systems.
BleepingComputer has sent MailChimp and Trezor further questions about the breach but has not heard back.


Comments
Icepop33 - 2 years ago
Thanks for bringing this to our attention. You usually hear it here first.
One question, though. Where the hell is everybody?
Some lively discussion would be nice. Maybe not my forte, but your site deserves more apparent traffic. I like your articles that are thorough and well-written with pertinent details including mitigation, if available at the outset. Keep up the good work!
As an aside, I think we are staring a hard truth in the face.. and that is that educating end users about best security practices (let's call it "wet tech", lol) seems to be the most reliable defense against institutional breaches and cyber threats in general, and yet we have to admit that there are not just some, but a vast majority that "we just can't reach" due to human nature, ingrained habits, gullible personalities, propensity for taking shortcuts to make work flow easier, resentment at being locked down by IT (hacker streak), human error, lack of sleep, criminal intent, etc., etc I think we are stuck with the paradigm of hunter and prey, white hats and black hats (and all hats in between) for the forseeable future, which ought to make the solution providers happy.
BloopingMoose - 1 year ago
Wow. This being RIGHT after the SAME THING happened on January 11th where 133 accounts were compromised!
That $12,000,000,000 sure seems like money well spent, doesn't it?